 cloud security is shared[/caption]
cloud security is shared[/caption]
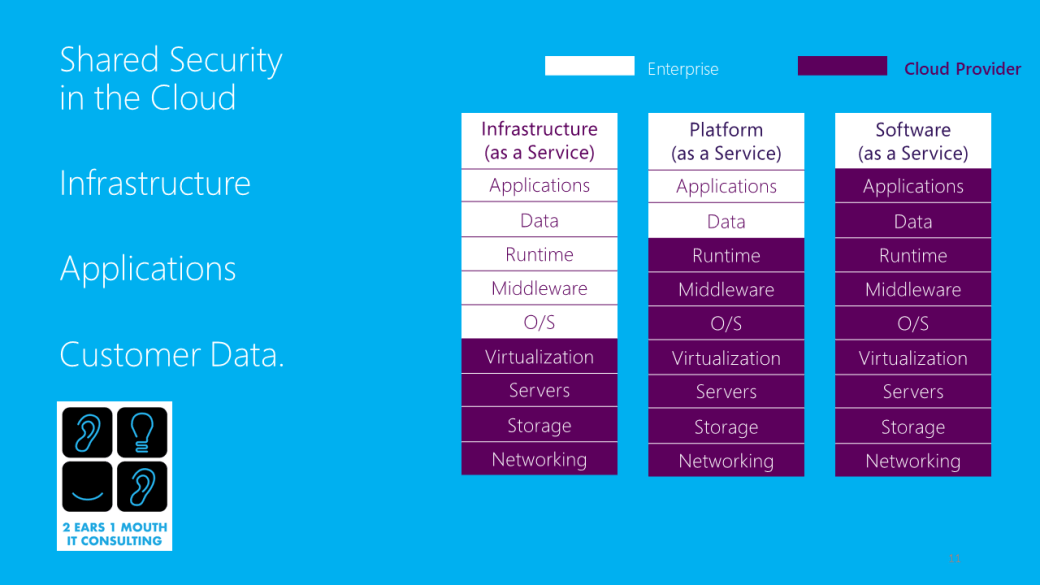
When I first became familiar with enterprise cloud computing, one of the primary objections of cloud adoption was the security of the data within the applications. Today that has changed; as cloud has matured it is now seen as an option for IT infrastructure that can be designed to be more secure than on premises solutions. Through the process of designing a cloud infrastructure IT professionals have become aware of the increase security benefits cloud offers. Concurrently, IT data exposure and breaches have become more widespread and security has become a greater responsibility. These factors have led all cloud architects, whether with a cloud provider or working within an enterprise, to realize that cloud security is a shared responsibility. Cloud security is shared in two respects, first within the different groups of the enterprise and secondly, the responsibility of securing data is split between the enterprise and the cloud provider. For the purpose of this article we will focus on the sharing of security responsibilities between the enterprise and the provider. I will segregate three categories of cloud computing responsibility in order to simplify the roles and responsibilities: infrastructure, operating systems including applications and customer data.
Private Cloud
Most IT users today consider a virtualize stack of IT infrastructure on premises a private cloud. In this scenario, as existed before cloud computing, the enterprise is responsible for all aspects of security. In an on-premises private cloud infrastructure the enterprise needs to secure their data from all physical, technical or administrative threats. With large organizations the security responsibilities can be shared within groups of their IT departments which may include network, security, application and compliance.
Infrastructure as a Service.
The greatest security coordination concerns come from a public or hybrid cloud configuration such as infrastructure as a service (IaaS). With an IaaS environment the enterprise has agreed to have the provider manage the infrastructure component of the IT security. This enables the enterprise to outsource all security and regulatory concerns concerning the actual server hardware. They also realize benefits of physical security because their IT infrastructure is off premises and in a secured facility. Many times, regulation or even large customers, will mandate an audited data center standard such as SOC 2 for their IT infrastructure as a requirement of the business partnership. Creating an audited SOC 2 compliant data center on premises can be costly and time-consuming. The hosting of their IT infrastructure in an audited and physically secure data center is one of the greatest benefits of IaaS.
Beyond the physical infrastructure, the IaaS or cloud provider also assures the security of the software hypervisor that orchestrates the virtualized cloud operating systems and services. However, the enterprise is still responsible for the operating systems of the virtual servers and the security patches the software developer issues for them. Additionally, the enterprise is responsible for the security of all their own software applications and the data that resides on them. Some cloud providers will offer managed services to their clients that will include security functions. The provider may offer a managed firewall, monitoring and even malware protection for the virtual servers they host. These services add value as the provider is more familiar with security best practices in the IT infrastructure stack than the enterprise. Still there is always a shared responsibility for security with the enterprise always responsible for their own data.
Software as a Service (SaaS)
SaaS is the cloud technology the majority of businesses have the most experience with and understand the best. Common SaaS platforms like Microsoft Office 365, Google G Suite or CRM based software like salesforce.com have made SaaS commonplace. Virtually the whole IT stack is owned by the provider in a SaaS platform, however, the enterprise still does still have security responsibilities. The enterprise’s primary security responsibility is concerned with their own data. The business owns their data and needs to ensure it is free of malware and other external threats. They also need to protect the end points such as laptops and tablets that are used to access the SaaS data.
Additional Considerations
Other IT security responsibilities the enterprise needs to consider in any Cloud environment are connectivity, authentication and identification services as well as managing abandoned resources.
Connectivity to the cloud provider is most secure when a private circuit or connection can be implemented. If a private connection is not practical the enterprise needs to create a secure connection such as a virtual private network (VPN) and assure a secure connection is created over public internet.
Authentication and identification of network users is an integral part of any enterprise IT network. Additionally, it is equally important to integrate any authentication or directory service with the cloud solution. A solution like Microsoft Azure AD is considered by many as a best practice for this complicated process. It was described in some detail in a previous article Active Directory (AD) in the Cloud. Finally, a frequent cause for concern, especially with enterprises that employ large IT staffs, are abandoned resources. These are cloud instances that were created and have lost their relevance and have been forgotten. They can reside in a public cloud for years, with continued billing, and the customers’ data is open to the public since they were created in a time with less stringent security policies. Periodic billing review and the monitoring services security platforms offer can eliminate this waste.
Business cloud solutions offered to the enterprise come in many different configurations that vary as to the type of infrastructure, software and services offered. In all cloud environments security requires a shared responsibility as well as a layered approach coordinated between the cloud providers and the enterprise. A supplier agnostic advisor like Two Ears One Mouth IT Consulting can assist by helping a business find the right provider and security services for your business’s applications.
If your business is unique and requires a custom cloud security solution for IT Support
Contact Jim Conwell (513) 227-4131 jim.conwell@twoearsonemouth.net
we listen first…